North Korean hackers are stepping up efforts to infiltrate cryptocurrency companies by posing as IT workers, raising fresh security concerns for the industry, according to Binance co-founder Changpeng “CZ” Zhao and a team of ethical hackers.
CZ sounded the alarm Thursday on X about the growing threat of North Korean hackers seeking to infiltrate crypto companies through employment opportunities and even bribing exchange staff for data access.
“They pose as job candidates to try to get jobs in your company. This gives them a “foot in the door,” specifically for employment opportunities related to development, security and finance, CZ said.
“They pose as employers and try to interview/offer your employees. During the interview, they will be a problem with Zoom and they will send your employee a link to an “update”, which contains virus that will takeover your employee’s device.”
Other North Korean agents give employees coding questions to send them malicious “sample code” later, pose as users to send malicious links to customer support, or even “bribe your employees, outsourced vendors for data access,” Zhao said.
“To all crypto platforms, train your employees to not download files, and screen your candidates carefully,” he added.
Related: Bitcoin ETFs are next major target for North Korean hackers — Cyvers
The warning follows similar concerns from Coinbase, which reported a new wave of threats last month.
In response, Coinbase CEO Brian Armstrong introduced new internal security measures, including requiring all workers to receive in-person training in the US, while people with access to sensitive systems will be required to hold US citizenship and submit to fingerprinting.

“We can collaborate with law enforcement […] but it feels like there’s 500 new people graduating every quarter, from some kind of school they have, and that’s their whole job,” Armstrong told Cheeky Pint podcast host John Collins.
Related: Bitcoin whale awakens after 12 years, transfers 1,000 BTC before US Fed meeting
Security Alliance uncovers 60 North Korean hackers impersonating IT workers
Zhao’s warning came as a group of ethical hackers called Security Alliance (SEAL) compiled the profiles of at least 60 North Korean agents posing as IT workers under fake names seeking to infiltrate US crypto exchanges and steal sensitive user data.
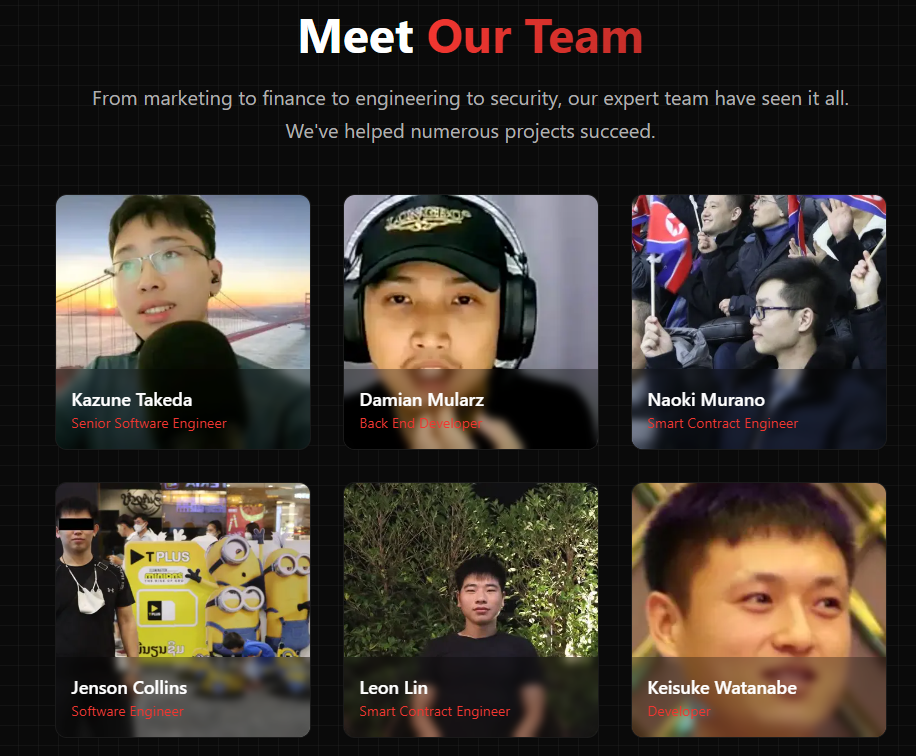
“North Korean developers are eager to work for your company, but it’s important to not get scammed by impostors when hiring,” Security Alliance said in a Wednesday X post, sharing its new repository for North Korean impersonators.
The repository contains key information on North Korean impersonators, including aliases, fake names and email used, along with websites, both real and fake citizenships, addresses, locations and the numbers of firms that hired them.
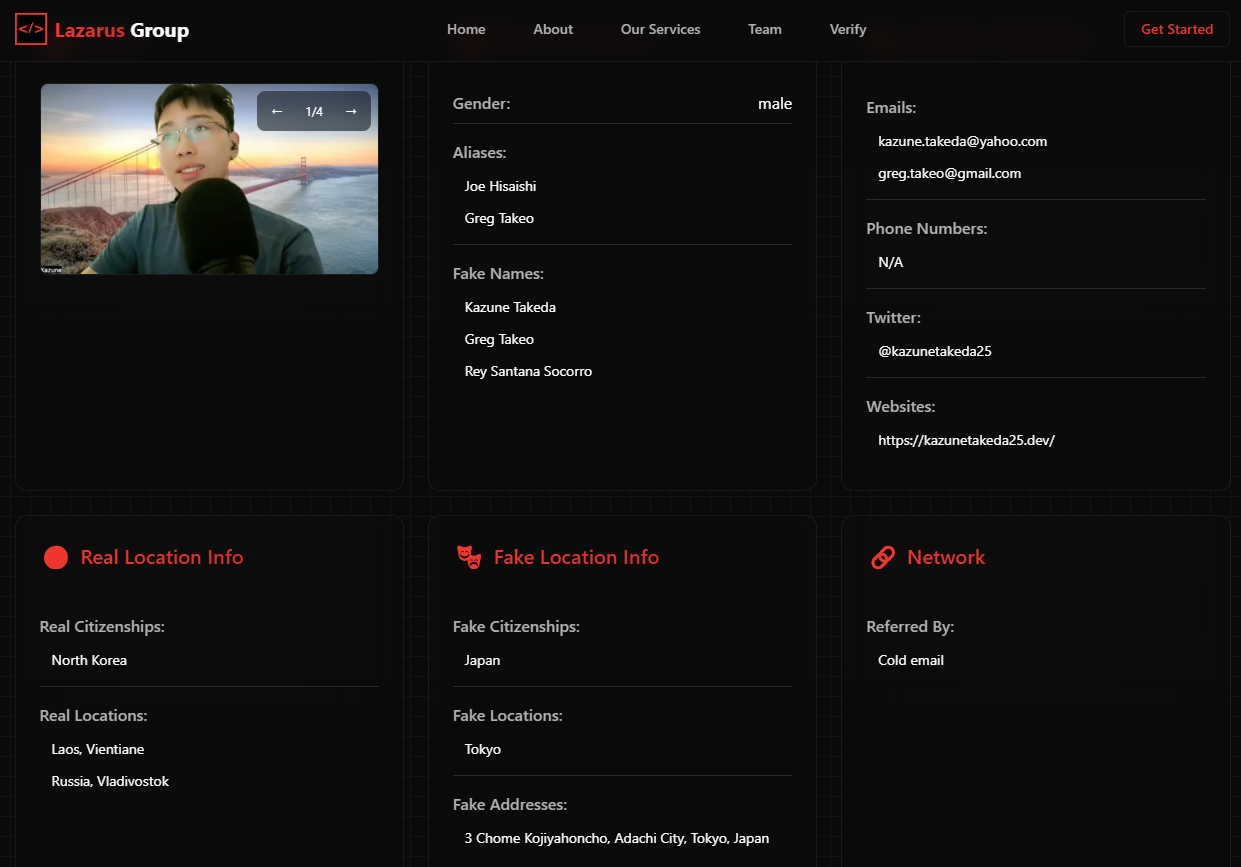
Salary details, GitHub profiles and all other public associations are also included for each impersonator.
In June, four North Korean operatives infiltrated multiple crypto firms as freelance developers, stealing a cumulative $900,000 from these startups, illustrating the growing threat, Cointelegraph reported.
The white hat SEAL team was formed to combat these exploits, led by white hat hacker and Paradigm researcher Samczsun. SEAL conducted more than 900 hack-related investigations within a year of its launch, illustrating the growing need for ethical hackers, Cointelegraph reported in August 2024.

North Korean hackers like the infamous Lazarus Group are the main suspects behind some of the most devastating cryptocurrency heists, including the $1.4 billion Bybit hack, the industry’s largest so far.
Throughout 2024, North Korean hackers stole over $1.34 billion worth of digital assets across 47 incidents, a 102% increase from the $660 million stolen in 2023, according to Chainalysis data.
Magazine: Coinbase hack shows the law probably won’t protect you — Here’s why