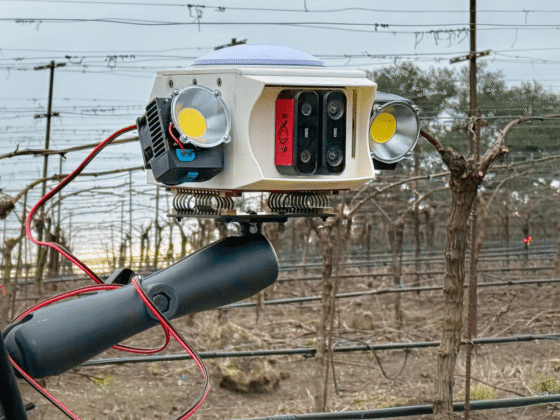
From sleek conferencing setups and smart classrooms to complex control rooms, audiovisual (AV) systems have become an essential part of how we work and communicate. But behind the interfaces lies an often-overlooked risk – security. Many AV systems still run on outdated software and firmware, creating vulnerabilities that attackers can exploit with relative ease.
Because AV equipment is not always seen as ‘business critical’ and is sometimes managed separately from the core IT infrastructure, it is frequently assumed to be safe – isolated on its own network or low risk by nature. But this complacency is dangerous. Many devices operate on older versions of software packages which are not always updated even when new versions are released for the device. This creates vulnerabilities in the system.
Chief Security Officer at Cinos.
Knowing the risks
While hybrid working has brought convenience it’s also increased risk. Remote access may speed up troubleshooting, but it also expands the attack surface. Social engineering attacks such as phishing can trick users into handing over access credentials, especially when awareness is low.
As cyber attackers become more sophisticated, they’re shifting their attention to overlooked entry points like AV infrastructure. A good example is YouTuber Jim Browning’s infiltration of a scam call center, where he used unsecured CCTV systems to monitor and expose criminals in real time. This highlights the potential for AV vulnerabilities to be exploited for intelligence gathering.
To counter these risks, organizations must adopt a more proactive approach. Simulated social engineering and phishing attacks can help assess user awareness and expose vulnerabilities in behavior. These simulations should be backed by ongoing training that equips staff to recognize manipulation tactics and understand the value of security hygiene.
In parallel, organizations that use third parties for remote support should be prioritize partners that undergo independent security audits such as ISO 27001 and Cyber Essentials Plus. These accreditations help ensure that strict controls are in place around remote access, including the use of secure management tools and clearly defined policies governing their use.
CVSS – a measured approach to risk
Not all AV vulnerabilities are created equal. That's where the Common Vulnerability Scoring System (CVSS) comes in. CVSS helps IT and AV teams prioritize their response by evaluating the complexity of an attack, the scope of its potential impact, and its effect on confidentiality, integrity, and availability.
Vulnerabilities with CVSS scores above 7.5 should prompt swift mitigation. Those rated at the maximum 10 out of 10 require immediate action due to their high severity and low complexity of exploitation. That said, patching these vulnerabilities isn’t always straightforward. In complex, interconnected AV environments, patching updates can introduce compatibility issues that disrupt operations. Organizations should adopt a measured, risk-based approach, balancing the likelihood of exploitation against operational stability.
The severity of breaches also depends on the device and its role. Compromised management interfaces or control code could allow attackers to manipulate systems or access other network devices. Exploited cameras and microphones can lead to breaches of video or audio data, posing serious privacy risks and enabling unauthorized surveillance.
Strengthening AV security
To mitigate the risks posed by vulnerable AV systems, organizations should take a proactive and layered approach to security. This includes regularly updating device firmware and underlying software packages, which are often left outdated even when new versions are available. Strong password policies should be enforced, particularly on devices running webservers, with security practices aligned to standards like the OWASP Top 10.
Physical access to AV infrastructure must also be tightly controlled to prevent unauthorized LAN connections. Where legacy protocols like SCP, SFTP, FTP, or Telnet are still in use, these should be hardened or disabled wherever possible. Encrypting communication between devices using modern protocols such as TLS 1.3, and ensuring appropriate cipher suites are in place, helps safeguard data in transit. Similarly, encrypting data at rest, whether configuration files, control code or temporary data, adds another layer of protection, limiting the damage that can result from a breach.
Collaboration is key
Ultimately, security is a shared responsibility. While network teams play a central role in defending infrastructure, leaving all security decisions to them can be shortsighted. Many vulnerabilities stem from device-specific issues such as outdated firmware, default configurations, or poorly managed passwords that cannot always be mitigated by network controls alone. Even a well-configured device can present risks if it’s connected to a poorly segmented or insecure network.
AV professionals, IT leads, and vendors need to collaborate closely, sharing expertise and intelligence to identify vulnerabilities and address integration challenges. AV teams must take an active role by ensuring devices are updated and properly configured before deployment, clearly communicating potential risks and requirements to network teams, and following best practices such as implementing VLANs, restricting unnecessary traffic, and enabling secure management protocols.
By working together, organizations can build a layered defense that addresses risks at both the device and network levels; strengthening the overall security posture and reducing the likelihood of a breach.
AV systems may not be the first thing you think of when you hear ‘cybersecurity risk’ and that’s exactly the problem. From data leaks and surveillance breaches to unauthorized lateral movement across networks, the consequences of ignoring AV security are real. It’s time to treat AV like the critical infrastructure it has become.
We've featured the best headset for working from home.
This article was produced as part of TechRadarPro's Expert Insights channel where we feature the best and brightest minds in the technology industry today. The views expressed here are those of the author and are not necessarily those of TechRadarPro or Future plc. If you are interested in contributing find out more here: https://www.techradar.com/news/submit-your-story-to-techradar-pro